
INVISIBILITY CLOAKING
CYBERSECURITY FABRIC
Cyber Bubble Technology
Zero Trust Network Access
Edge IoT
Cybersecurity Management
Cybersecurity
Mesh Architecture
Why Cylentium
Technology conceived in the Cybersecurity Cyberwarfare Labs of the US Naval Postgraduate School (NPS) for “Cloaking & Invisibility” for US Naval Ships, military operations, and other environments
Original Founding Member for 802.1xx, MACsec, iEEE, and FIPS Standards Organizations
IEEE Member & Certified Global Authority for the Design & Deployment of unique custom global network protocols
Solutions
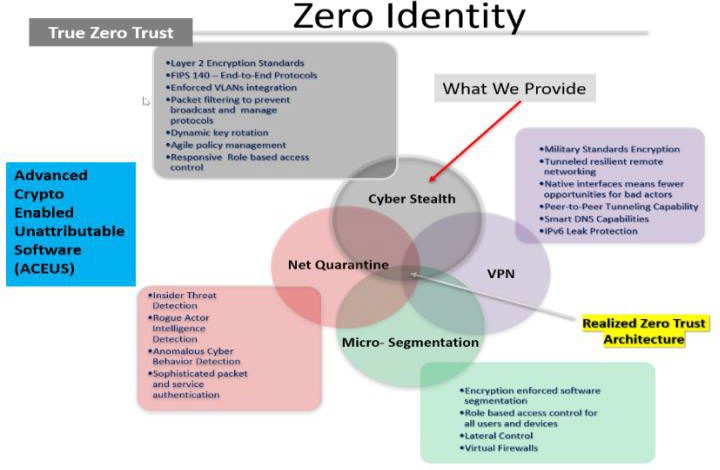
We secure data from start to finish and in transit (Secure Access Service Edge in Layer 2) by using a proprietary end to end encrypted Layer-2 network protocol. Our packet design and encryption software makes targeting and tracking network traffic increasingly difficult by making IP addresses virtually invisible on any connected device.
Our software is a multi-layer product that combines a military grade VPN, Identity Management through automated device and user micro-segmentation Anomalous Behaviour Tracking and Cyber Invisibility through Layer 2 encrypted data traffic and secure network protocol.
We are the next generation of VPN.
We are cyber invisibility.
Intelligence
Zero Identity Invisibility Protection for Defense & Defense Systems, Intelligence Agencies, and Government Operations
Industry 4.0
The Fourth Industrial Revolution is the ongoing automation of traditional manufacturing and industrial practices, using modern smart technology. We provide Zero Identity Invisibility Protection for those sophisticated ICS & SCADA environments
Enterprise
END-TO-END Zero Identity Invisibility Protection for Enterprises, Small & Medium Businesses, and Entrepreneurs. Ideal for Remoting Working environments.
Home / Consumer
Zero Identity Invisibility Protection for your family, your home, smart home automation, and personal electronics and communications
Cylentium
Cylentium is the World's First & Only Zero Identity CyberSecurity Bubble Technology
CylentiumHome
CylentHome is the first Zero Identity CyberSecurity Bubble that protects your Family and all Smart Home Devices
CylentiumNQ
CylentNQ- Net Quarantine - monitors and detects for intrusions by any device. When detected, NQ quarantines the intruder, and alerts you to is presence and status
CylentiumTravel
CylentTravel is your small travel cybersecurity device. The size of the palm of your hand, plug it into the internet from anywhere in the world, and you are protected inside a non-detectabe bubble of Zero Identity Cyber Invisiblity